As organizations adopt cloud platforms, remote work models, and distributed IT infrastructures, traditional security approaches are becoming less effective.
For many years, cybersecurity relied on a perimeter-based model where anything inside the corporate network was automatically trusted. However, modern cyber-attacks have shown that this assumption can create serious vulnerabilities.
Zero Trust Architecture addresses this issue by removing implicit trust from the network and requiring verification for every access request.
What is Zero Trust Architecture?
Zero Trust is a cybersecurity framework built on a simple but powerful principle:
Never trust, always verify.
Under this model, every user, device, and system must continuously prove its legitimacy before gaining access to resources.
Access decisions are based on multiple factors such as:
- User identity
- Device security status
- Location and behavior patterns
- Access policies and permissions
- This approach significantly reduces the risk of unauthorized access and data breaches.
Core Principles of Zero Trust
Identity Verification
Identity is the foundation of Zero Trust security. Every user must authenticate through strong identity verification methods such as multi-factor authentication, biometric verification, or security tokens.
Device Security:
Before granting access, devices must meet strict security standards. Endpoint protection systems ensure that devices are updated, protected, and compliant with organizational policies.
Least Privilege Access:
Zero Trust enforces the principle of least privilege, meaning users only receive the minimum permissions necessary to perform their tasks. This limits the damage that can occur if an account is compromised.
Continuous Monitoring:
Security systems continuously monitor network activity, user behavior, and system interactions. Suspicious activity can be detected quickly and access can be revoked immediately.
Micro-Segmentation:
Instead of a single trusted network, Zero Trust divides infrastructure into smaller segments. Each segment requires independent authentication and authorization, preventing attackers from moving freely across systems.
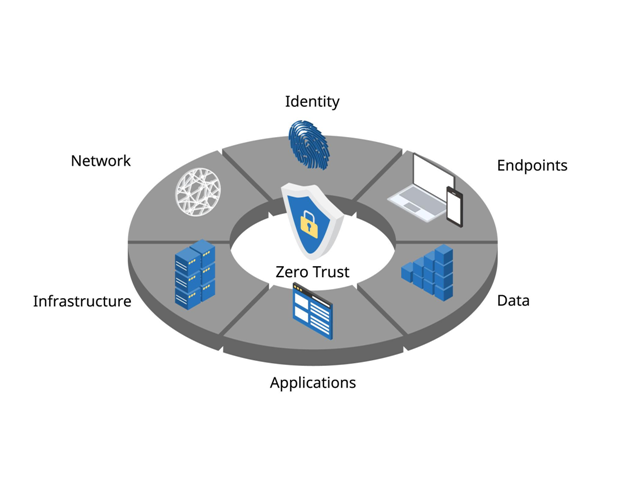
Key Components of a Zero Trust Environment
A complete Zero Trust architecture protects several layers of the digital ecosystem.
Identity
Ensures that users are authenticated and authorized before accessing systems.
Endpoints
Verifies that devices such as laptops, smartphones, and servers meet security requirements.
Applications
Protects business applications with authentication and strict access policies.
Data
Sensitive information is encrypted and protected regardless of where it is stored.
Infrastructure
Servers, databases, and cloud environments enforce strict access control rules.
Network
Network communications are monitored and secured to prevent unauthorized access.
Why Organizations Are Adopting Zero Trust
Cyber threats are becoming increasingly sophisticated. Attackers are no longer limited to external breaches; insider threats and compromised credentials are also common.
Zero Trust helps organizations improve their security posture by:
- Reducing the attack surface
- Preventing unauthorized lateral movement
- Strengthening identity-based security
- Improving visibility across systems
- Supporting secure remote work environments
- These benefits make Zero Trust an essential strategy for modern enterprises.
